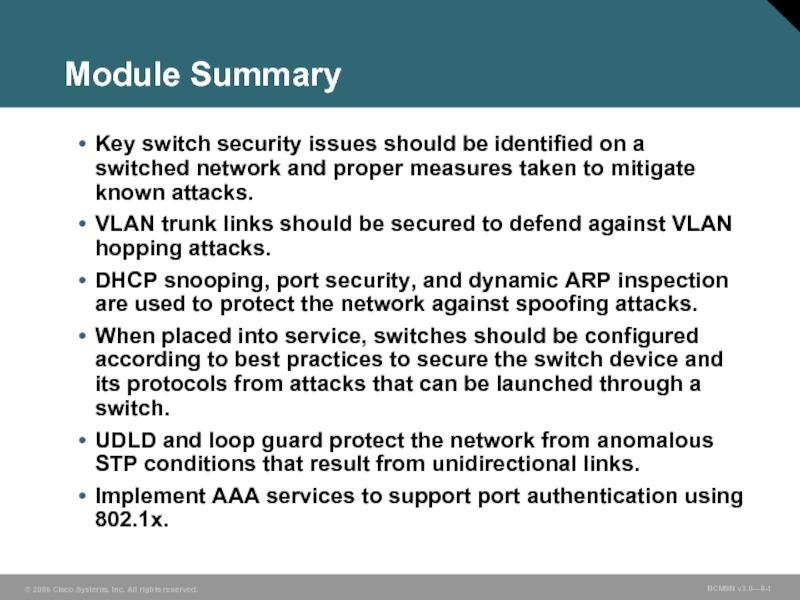
network and proper measures taken to mitigate known attacks.
VLAN trunk links should be secured to defend against VLAN hopping attacks.
DHCP snooping, port security, and dynamic ARP inspection are used to protect the network against spoofing attacks.
When placed into service, switches should be configured according to best practices to secure the switch device and its protocols from attacks that can be launched through a switch.
UDLD and loop guard protect the network from anomalous STP conditions that result from unidirectional links.
Implement AAA services to support port authentication using 802.1x.
- Главная
- Разное
- Дизайн
- Бизнес и предпринимательство
- Аналитика
- Образование
- Развлечения
- Красота и здоровье
- Финансы
- Государство
- Путешествия
- Спорт
- Недвижимость
- Армия
- Графика
- Культурология
- Еда и кулинария
- Лингвистика
- Английский язык
- Астрономия
- Алгебра
- Биология
- География
- Детские презентации
- Информатика
- История
- Литература
- Маркетинг
- Математика
- Медицина
- Менеджмент
- Музыка
- МХК
- Немецкий язык
- ОБЖ
- Обществознание
- Окружающий мир
- Педагогика
- Русский язык
- Технология
- Физика
- Философия
- Химия
- Шаблоны, картинки для презентаций
- Экология
- Экономика
- Юриспруденция